How to mix ETH with tornado.cash
Disclaimer
This summary is intended for educational purposes. Most of the parts shown are still heavily under construction and might not work as expected.
You should have some basic experience with crypto currencies as a user e.g. know how to receive and send transactions.
If you are a developer and familiar with underlying concepts of blockchains and most crypto currencies, you will not learn much in the video.
Here is a list of all mentioned links and products from the video plus some stuff for further reading if you are interested in more details.
Used resources in this video:
- tornado.cash: https://tornado.cash/
- Metamask: https://metamask.io/
- Etherscan: https://etherscan.io/
Further reading / viewing / consider using:
- Basic knowledge how blockchains work: https://www.youtube.com/watch?v=bBC-nXj3Ng4
- Click through video from tornado.cash: https://youtu.be/cbpwf6ESr0s
- What is fiat money (spoiler: your $ £ €): https://en.wikipedia.org/wiki/Fiat_money
- TOR browser: https://www.torproject.org/
- Brave browser: https://brave.com/
- Monero: https://web.getmonero.org/
- ZCash: https://z.cash/
- Wikipedia: zero knowledge proofs incl. the „Ali Baba cave“ and „the two balls and the color-blind friend“ examples
- zk-SNARKs: Link to an intro article
Some quick notes ahead
- Ethereum (Ether, ETH, Ξ) is not meant to be anonymous
- Governments are working on making all transactions completely transparent and easy traceable for prosecution
- Mixers like tornado.cash try to obfuscate origins and destinations of transactions
- All transactions are bits of a puzzle, even when you are using tornado.cash for a certain part of your transaction chain, there are still parts left with which an attacker might try to deanonymize you
- Monero (https://web.getmonero.org/)
- ZCash (https://z.cash/)
Part 1: why?
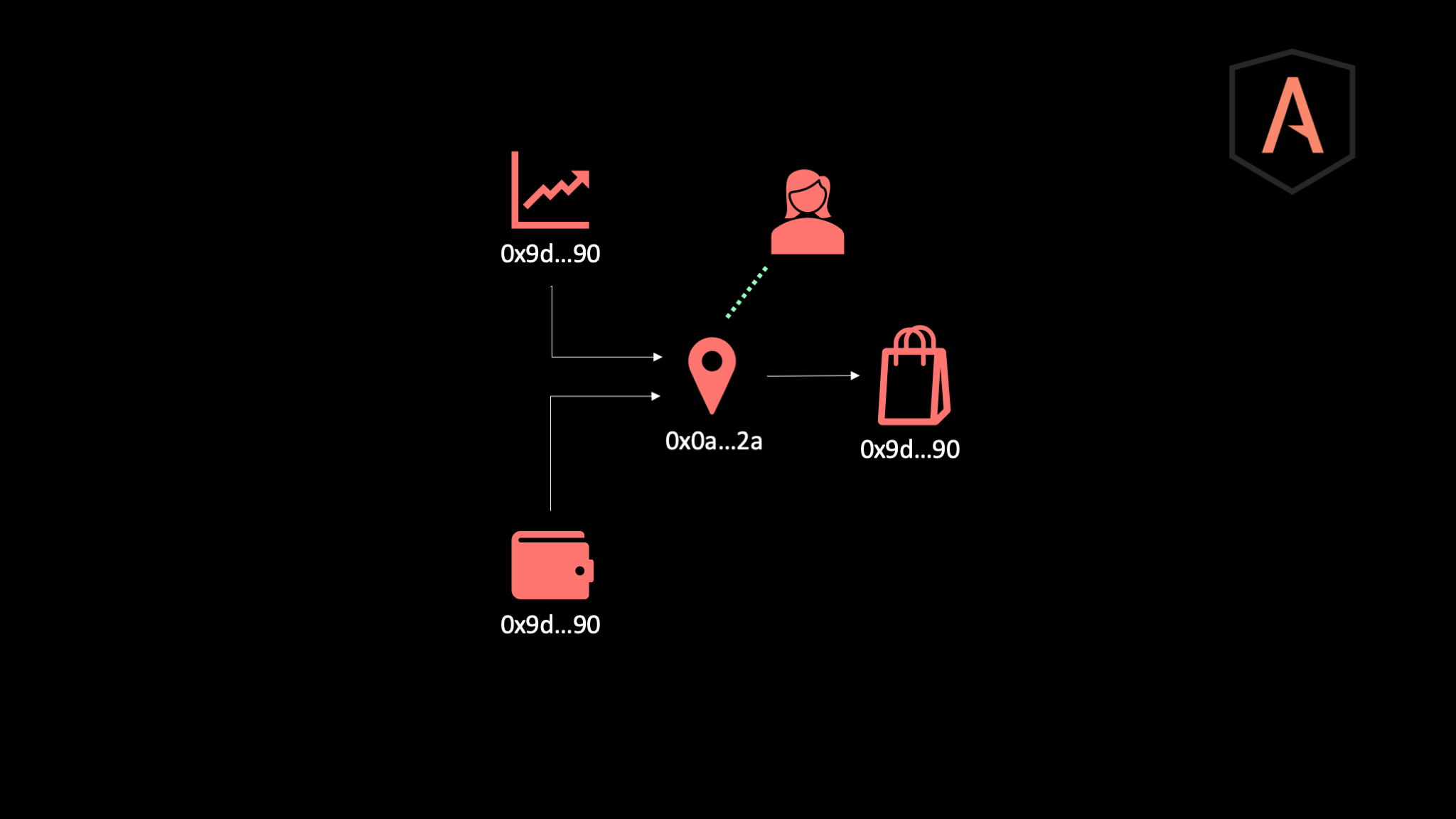
It‘s all about addresses and transactions (Tx). An address of an exchange looks like:
0x9D96b0561be0440eBE93e79FE06a23BBe8270f90
A random chosen real transaction looks like:
0xa8c4f21c83d8eafd7a0945ab0261798a46dc13a2e76aac695cb9bf1d615e6805
As a human you might say that this is anonymous because you cannot do anything with these long random codes. But there are crowd sourced databases like https://etherscan.io/ which reveal a lot of information. Governments and big enterprises can collect even more data. More data in this case means more knowledge, better identification and precise balance info.
When you buy ETH in exchange to fiat currencies your identity is saved (e.g. PII, photo, video, id, credit card, etc.). When you sell stuff online at least parts of your information are stored. If you buy stuff online that is the same. The more information is available the stronger the link between you and an ETH address gets.
Part 2: meta data and basic security
Making transactions transparent is all about linking collected data and information with an ETH address and getting the person’s identity who is behind this address. Always keep in mind that there are many ways of collecting data and metadata matters.
- Don’t do all steps from one and specially not your home IP address
- Take care about trackers and fingerprinting methods
- Take care about linked resources and content (even tornado.cash uses youtube and google fonts, be careful!)
- A good starting point is using the TOR or brave browser with all shields up
Use hardware tokens for your ETH addresses which hold your funds. Never ever keep your funds for a longer time at an exchange. When the exchange gets hacked you lose everything.
Writing secrets down on paper is saver than storing them online or in any digital device. A hacker might find your passwords and codes online but will never come to your home and find that one piece of paper where a code is written on. This is valid for most of the users. If you are a high-profile target, then you neither online nor in the physical world save.
Part 3: how mixers work
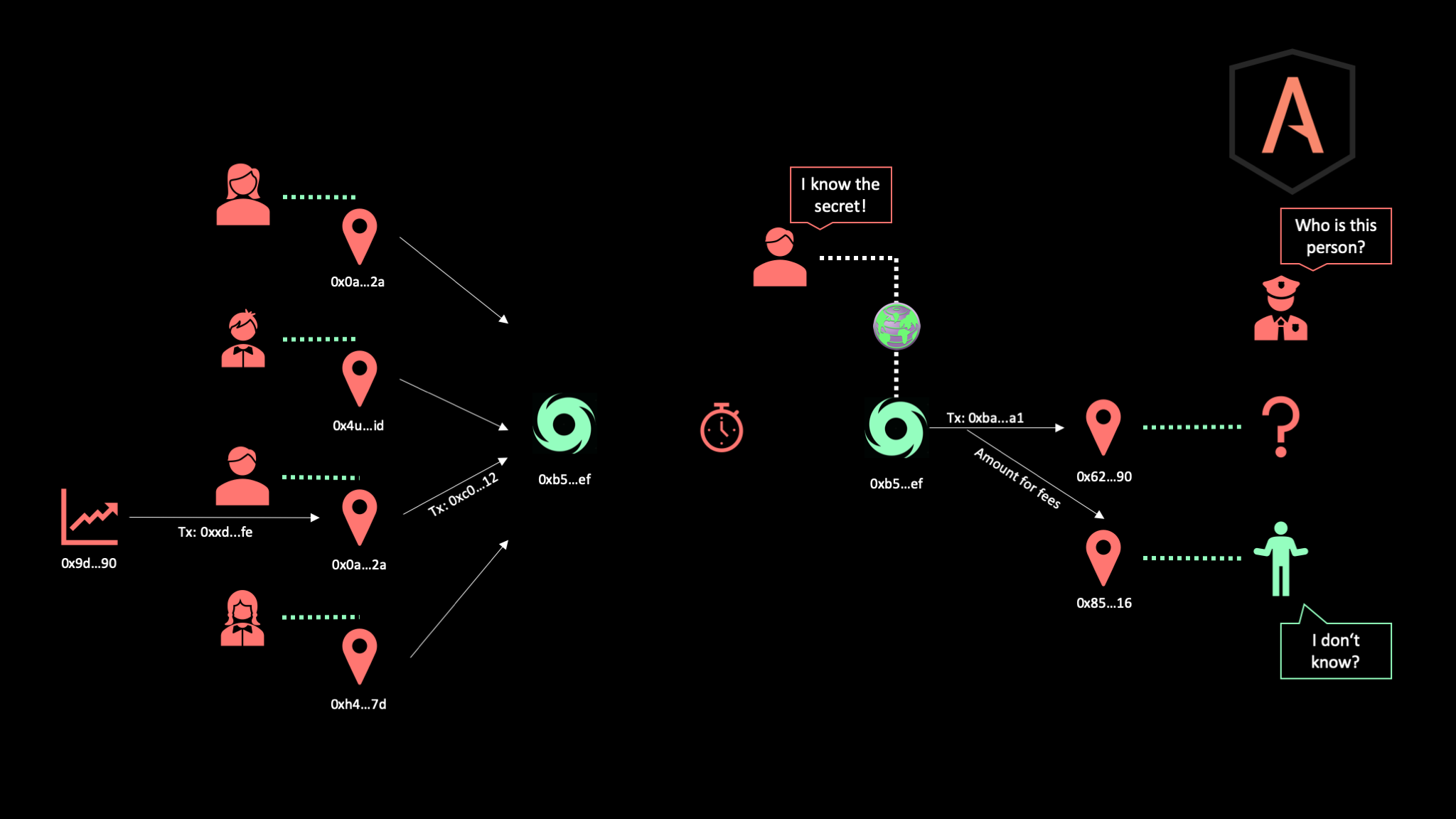
Mixers try to combine funds from different sources mix them and send the amount to an anonymous destination address. Doing so should cut the connection between an address holding ETH funds and your identity. Sending money to an anonymous destination address requires zero knowledge proofs as otherwise personal information like usernames and passwords would again be required to validate that you actually own a certain amount of ETH.
When you are using a mixer like tornado.cash you still receive ETH the same way as usual: trading fiat currencies, selling stuff online, etc. The address where you get the funds send to is pretty clear connected to your identity. But now you send the funds into a smart contract of tornado.cash. Important is: if you would be only one person doing this it would be like a card deck with only one card. You can mix as often as you want: it’s always the one card you’ll see and you would be always easy identified.
So many people should do this to increase the effort required for deanonymization. The online UI of tornado.cash shows the number of users in the current anonymity set and alerts you when you don’t wait long enough before you withdraw your funds.
One important reminder: metadata matters! If you do all from one IP, without using TOR or other Proxies as well as tracking preventing addons it’s pointless. A connection between all dots could be made through your IP address.
Also pointless is the direct withdraw option to a new wallet address, as this address has to pay for transaction fees, thus must have gotten some ETH from somewhere which likely links the address to your identity. The “relayer” option is the one to go for when withdrawing funds. The fees will be payed by the relayer, thus the amount send by the tornado.cash contract will be split, a small part goes to the tornado.cash relayer for the fees, and the rest to the shiny new address which nobody can link to your identity.
A few words about zero knowledge proofs. They are basically all about 3 things:
- Proofing to someone that you know a secret without revealing the secret
- That person could tell if you’re honest or not without knowing the secret
- Avoiding that any watching 3rd party will see that you know anything at all
In the tornado.cash example this means:
- The UI proofs to the tornado.cash contract that you know the secret note without sending it
- The tornado.cash contract can determine if you’re the owner of the transaction
- Any monitoring party will not be able to tell if you’re the owner or not (take care about your meta data)
For more details & examples: see Wikipedia, read about the „Ali Baba cave“ or „the two balls and the color-blind friend“ examples (both on the same wiki page), or even read the specs for zk-SNARKs (Link to an intro article).
Part 4: and now, what should I do?
You can decide based on your thread model. That is what most people do. If you are not in danger or don’t care at all what big enterprises know about you, things like tornado.cash are not of your interest.
From my point of view, we as a group and society have a responsibility for those who need anonymity to be save. The more people who actually care about anonymity should use tools like TOR, tornado.cash or similar solutions to be save on the internet and to help also people who really need anonymity. If only two persons use tornado.cash and both really need anonymity, it’s pretty easy to find out who they are. But finding two persons in a hundred or thousands is much more difficult. Like the needle in a haystack.
Also, our history proofs: when those “who have nothing to hide” don’t stand up for their privacy, there will be one point in time when there is nobody left who can standup for their rights when privacy has gone.